APT44, also known as the Sandworm Team, is a notorious cyber threat actor linked to disruptive attacks worldwide. From shutting down Ukraine’s power grid to deploying destructive malware, their operations demonstrate highly advanced tactics.
In this analysis, we use MITRE ATT&CK to map their techniques, uncover attack patterns, and extract actionable insights into their tradecraft. Understanding these methods is essential for strengthening cybersecurity defenses against persistent threats..
Sherlock Scenario:
Being in the ICS Industry, your security team always needs to be up to date and should be aware of the threats targeting organizations in your industry. You just started as a Threat intelligence intern, with a bit of SOC experience. Your manager has given you a task to test your skills in research and how well can you utilize MITRE Att&ck to your advantage. Do your research on Sandworm Team, also known as BlackEnergy Group and APT44. Utilize MITRE ATT&CK to understand how to map adversary behavior and tactics in actionable form. Smash the assessment and impress your manager as Threat intelligence is your passion.
According to the sources cited by MITRE, in what year did the Sandworm Team begin operations?

Answer: 2009
MITRE notes two credential access techniques used by the BlackEnergy group to access several hosts in the compromised network during a 2016 campaign against the Ukrainian electric power grid. One is LSASS Memory access (T1003.001). What is the Attack ID for the other?
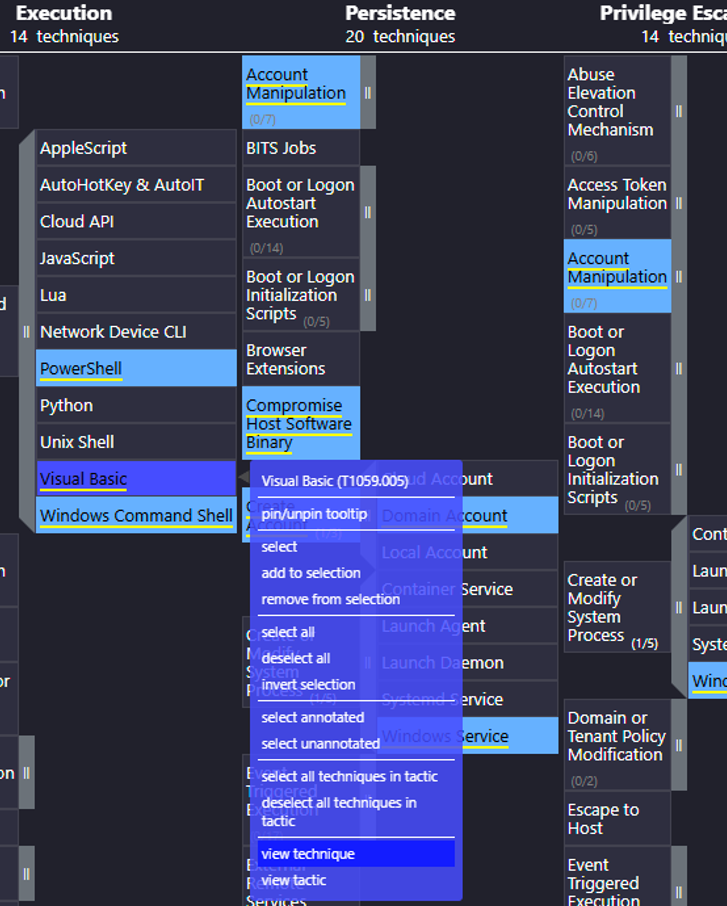
To analyze this, we need to examine the ATT&CK Navigator for this attack.

Answer: T1110
During the 2016 campaign, the adversary was observed using a VBS script during their operations. What is the name of the VBS file?
From there we can read the detailed report where the information is found:

The VBS script facilitated the lateral transfer of ICS-specific payloads, like 101.dll, across targeted systems.
Answer: ufn.vbs
The APT conducted a major campaign in 2022. The server application was abused to maintain persistence. What is the MITRE Att&ck ID for the persistence technique was used by the group to allow them remote access?
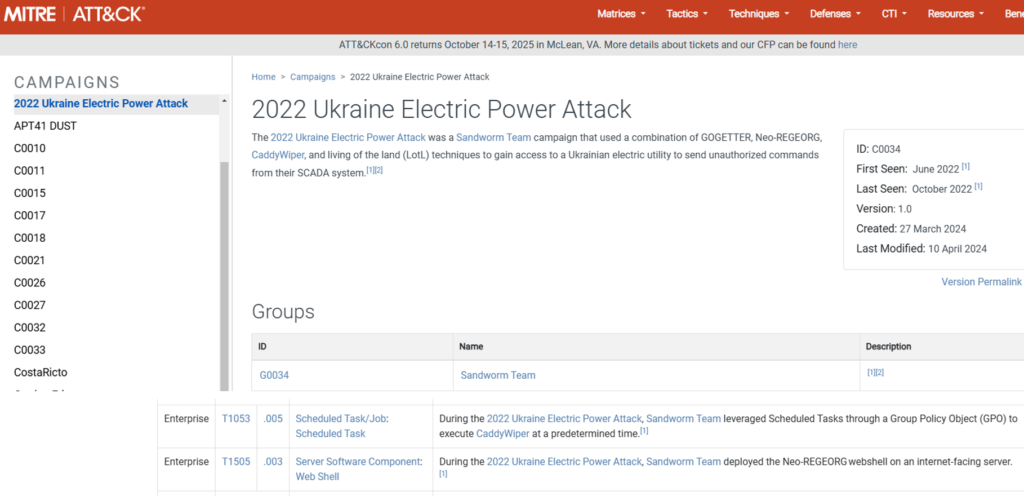
Answer: T1505.003
What is the name of the malware / tool used in question 4?
Answer: Neo-REGEORG
Which SCADA application binary was abused by the group to achieve code execution on SCADA Systems in the same campaign in 2022?
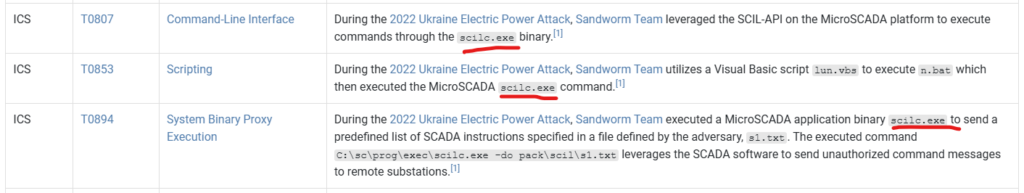
Answer: scilc.exe
Identify the full command line associated with the execution of the tool from question 6 to perform actions against substations in the SCADA environment.
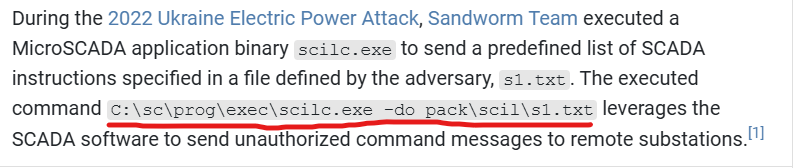
Answer: C:\sc\prog\exec\scilc.exe -do pack\scil\s1.txt
What malware/tool was used to carry out data destruction in a compromised environment during the same campaign?
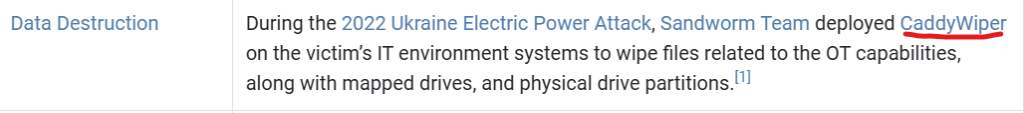
Answer: CaddyWiper
The malware/tool identified in question 8 also had additional capabilities. What is the MITRE Att&ck ID of the specific technique it could perform in Execution tactic?

Answer: T1106
The Sandworm Team is known to use different tools in their campaigns. They are associated with an auto-spreading malware that acted as a ransomware while having worm-like features .What is the name of this malware?
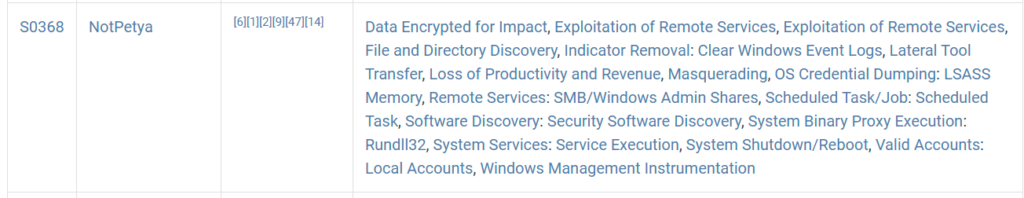
Answer: NotPetya
What was the Microsoft security bulletin ID for the vulnerability that the malware from question 10 used to spread around the world?

Answer: MS17-010
What is the name of the malware/tool used by the group to target modems?

Answer: AcidRain
Threat Actors also use non-standard ports across their infrastructure for Operational-Security purposes. On which port did the Sandworm team reportedly establish their SSH server for listening?
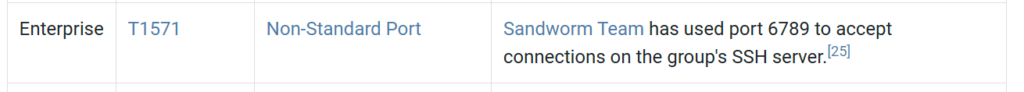
Answer: 6789
The Sandworm Team has been assisted by another APT group on various operations. Which specific group is known to have collaborated with them?

Answer: APT28
Summary
APT44, also known as the Sandworm Team, remains one of the most dangerous cyber threat actors, particularly targeting critical infrastructure. Their attacks, ranging from Ukraine’s power grid disruption to data-wiping malware campaigns, showcase highly sophisticated tactics. By leveraging MITRE ATT&CK, we mapped their techniques, revealing how they conduct credential theft, lateral movement, and ICS-specific attacks.
Understanding these methods is crucial for strengthening cybersecurity defenses, improving threat intelligence, and proactively mitigating risks posed by such advanced adversaries. As cyber threats continue to evolve, staying ahead with actionable intelligence is the key to resilience.

